Learn how to boost your mobile security and protect your digital identity. This tech blog will run through different forms of malicious software on your iOS or Android handset, the warning signs of a spyware infection, and how to remove such pestilence from your mobile devices if it is possible to do so. The emails […]
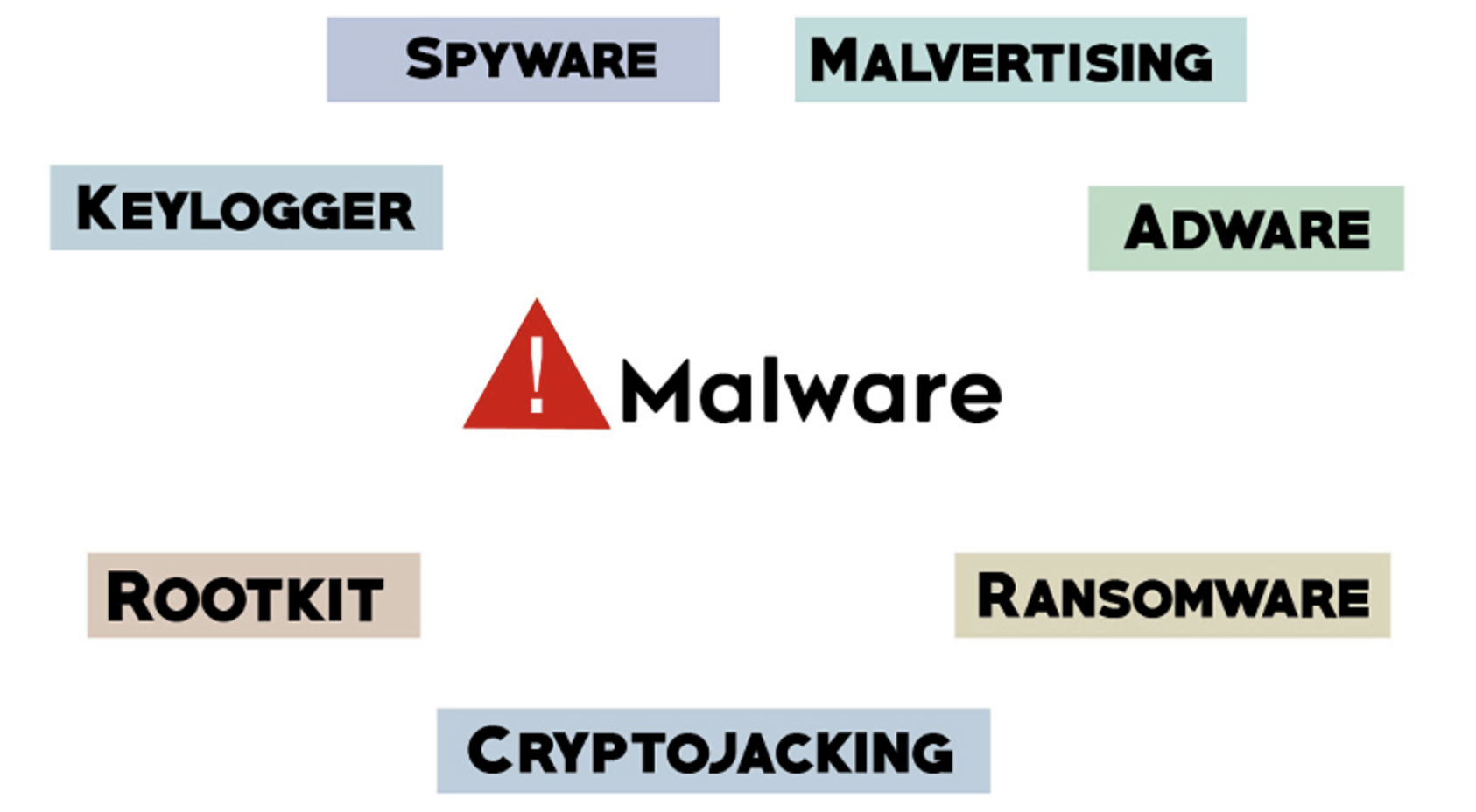
Malware typically refers to malicious software comprised of worms, viruses, Trojans, and several other harmful programs. Hackers and spammers use Malware to damage your data and gain access to your confidential and sensitive information. While no device is immune to malicious software or infections there are effective security practices you can implement to help prevent […]
Microsoft has continued its analysis of the LemonDuck coin-mining malware which has been crafted by some very determined, financially motivated cybercriminals. LemonDuck is known for installing crypto-miners in enterprise environments and has a well-stocked arsenal of hacking tools, tricks and exploits. Their goal is to have their malware retain exclusive access to a compromised network for as long as possible. The attackers try […]