Exploiting security flaws is one of the major tactics used by cybercriminals to attack organizations. Vulnerabilities are an unfortunate fact of life for operating systems, applications, hardware devices and databases. An attack against a database can easily compromise sensitive and confidential user and customer data. Based on analysis fromImperva covering 27,000 on-premises databases around the […]
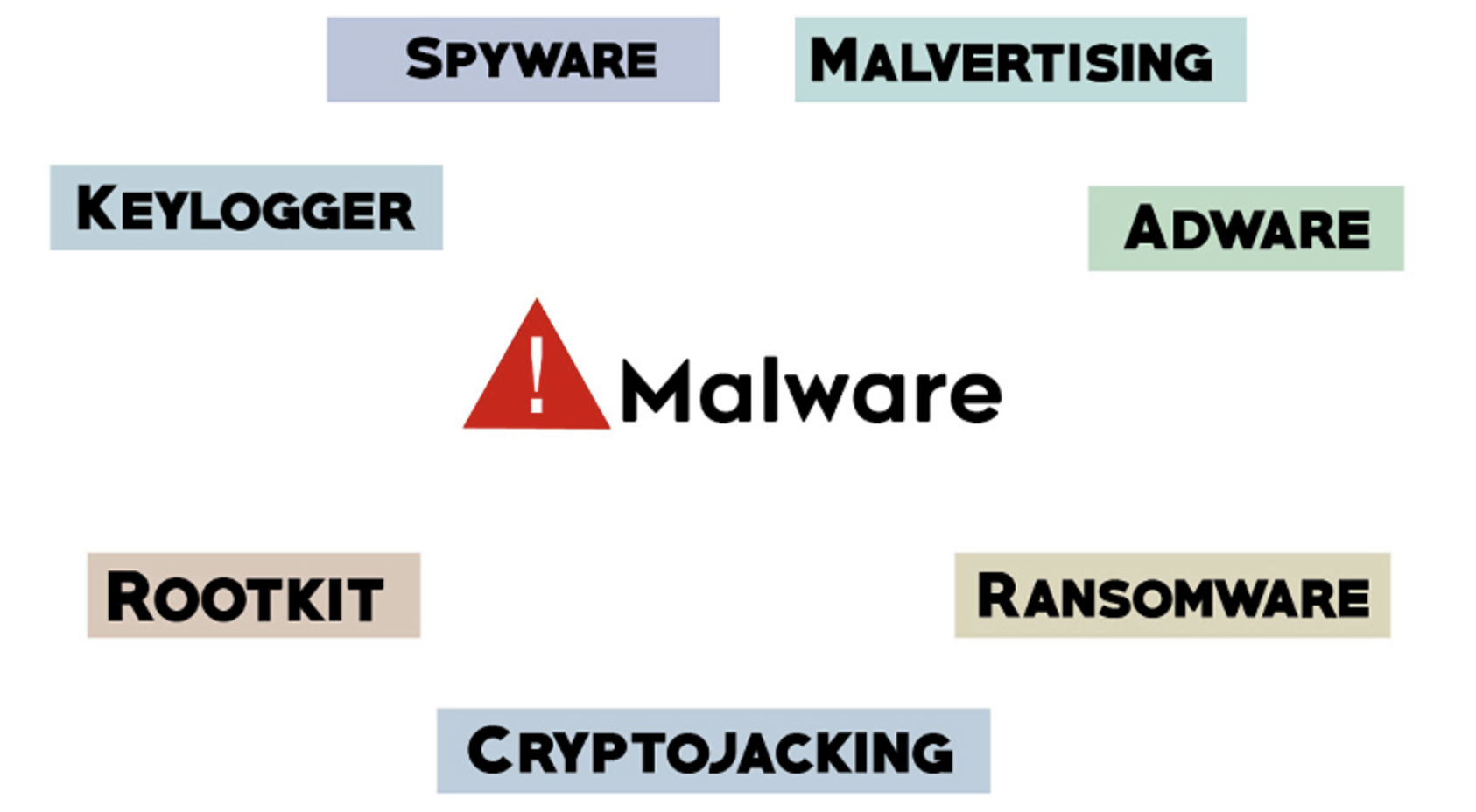
Malware typically refers to malicious software comprised of worms, viruses, Trojans, and several other harmful programs. Hackers and spammers use Malware to damage your data and gain access to your confidential and sensitive information. While no device is immune to malicious software or infections there are effective security practices you can implement to help prevent […]
1. Cyberattacks Affect All People Cyberattacks are so common in today’s world and recent reports show that hackers attack a computer in the US every 39 seconds! Once an attack happens millions of people could be harmed, businesses could be forced to shut down, and operations could be halted. Cyberattacks can happen on a global scale […]
Many companies want Internet of Things (IoT) devices to monitor and report on events at remote sites, and this data processing must be done remotely. The term for this remote data collection and analysis is edge computing. Edge computing refers to generating, collecting, and analyzing data at the site where data generation occurs, and not […]
Since most laptops have shifted to USB-C chargers, it makes it easier than ever to pick up a charger for your laptop so that you’re never without power. Most laptops come with a charger, and that charger is usually good enough for the job, but it can be very convenient to have a second charger. Here […]
For most people using your computer is apart of your everyday life and when it starts to act up and slow down it causes issues in your productivity and efficiency. If you are using Windows 7, 8, or 10 and have issues, Here are the top 10 tips to speed up your PC: 1. Programs Your Not […]
Microsoft released Excel 4.0 for Windows 3.0 and 3.1 in 1992 and many companies still use this functionality in legacy operations. The issue is that bad actors have started using Excel sheets and macros as a new way to deliver malware. Tal Leibovich, head of threat research at Deep Instinct, which is a cybersecurity company specializing in endpoint […]
Have you ever lost your data due to a computer crash, virus, or other disaster? Without a backup in place, data loss actually puts many organizations out of business because they just can’t recover. When a business suffers data loss, it means downtime and every hour of downtime is costing you money and missed opportunities. […]
Security vulnerabilities in millions of Internet of Things (IoT) devices, including connected security cameras, smart baby monitors and other digital video recording equipment, could allow cyber attackers to compromise devices remotely, allowing them to watch and listen to live feeds, as well as compromise credentials to prepare the ground for further attacks. The vulnerabilities in IoT devices that use […]