HP unveiled new software and cloud-based services designed to help IT teams manage and automate a slate of different tasks. HP Adaptive Endpoint Management is available now, and the tools were created with hybrid work in mind. Employee device management has become exponentially more difficult since remote work was embraced due to the COVID-19 pandemic. HP is helping customers take […]
Microsoft brings users a great operating system for personal computers, and while it has built-in security features they are not enough to fully protect yourself. Therefore, you need to improve the security level of your computer, which will make it more secure against viruses, malware, other malicious programs and even hackers. Here are the top […]
Exploiting security flaws is one of the major tactics used by cybercriminals to attack organizations. Vulnerabilities are an unfortunate fact of life for operating systems, applications, hardware devices and databases. An attack against a database can easily compromise sensitive and confidential user and customer data. Based on analysis fromImperva covering 27,000 on-premises databases around the […]
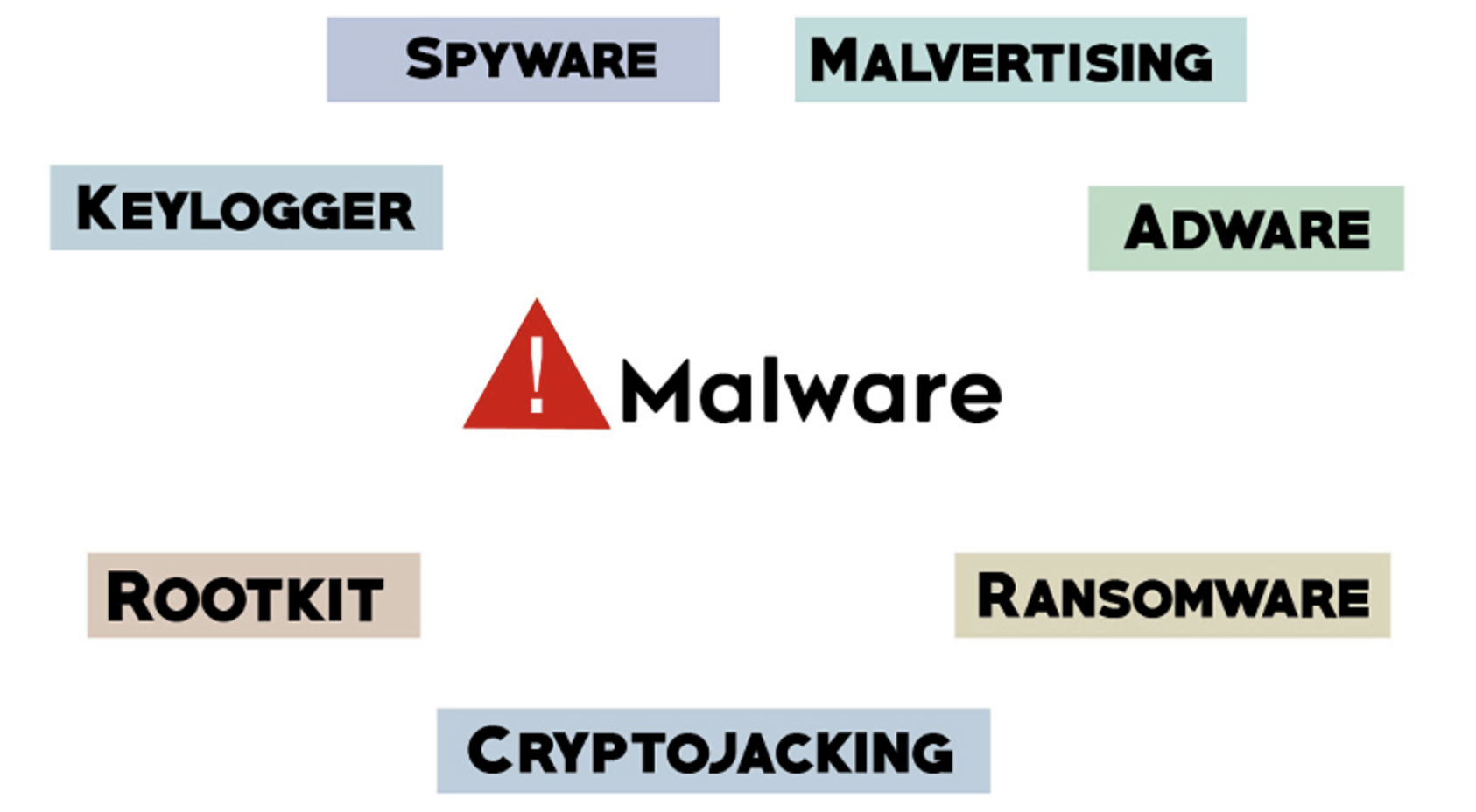
Malware typically refers to malicious software comprised of worms, viruses, Trojans, and several other harmful programs. Hackers and spammers use Malware to damage your data and gain access to your confidential and sensitive information. While no device is immune to malicious software or infections there are effective security practices you can implement to help prevent […]
Security vulnerabilities in millions of Internet of Things (IoT) devices, including connected security cameras, smart baby monitors and other digital video recording equipment, could allow cyber attackers to compromise devices remotely, allowing them to watch and listen to live feeds, as well as compromise credentials to prepare the ground for further attacks. The vulnerabilities in IoT devices that use […]
Preparing and approving the cybersecurity budget is an important responsibility for IT security executives. The budget has a direct impact on the organization’s ability to avoid or overcome cyberattacks. If the cybersecurity budget fails to cover all key bases, the organization could be forced to spend more on recovering from the cyberattack. While the obvious cybersecurity expenses […]
Hackers are using weak and stolen credentials in a significant way to compromise business-critical environments. Stealing access to your environment using a known password for a user account is a much easier way to compromise systems than relying on other vulnerabilities. Therefore, using good password security and robust password policies is an excellent way for organizations […]
Bad passwords are easy to remember, but also easy to guess and that can give an attacker access to your online accounts. That’s why the UK’s National Cyber Security Centre (NCSC) recommends that users pick three random words for a password rather than meeting complex requirements, such as an alphanumeric string, that could permit the creation of bad passwords like “pa55word.” One of […]
PunkSpider is scanning every website in the world to find and then publicly release their exploitable flaws all at the same time in the name of making the web more secure. PunkSpider automatically identifies hackable vulnerabilities in websites, and then allows anyone to search those results to find sites susceptible to everything from defacement to data […]